How to Protect Your Personal Data from Hackers: A Complete Cybersecurity Guide
In today’s hyper-connected digital world, personal data has become one of the most valuable commodities. From social media accounts to online banking, emails, and cloud storage — our daily lives are deeply integrated with the internet. However, with convenience comes risk. Cybercriminals are constantly looking for opportunities to exploit vulnerabilities and steal sensitive information.
This comprehensive cybersecurity guide will help you understand the methods hackers use and the best ways to protect your personal data effectively.
Understanding the Importance of Personal Data Security
Every time you go online, you leave digital footprints. These include your personal details, location data, browsing habits, payment information, and even private messages. Hackers target this information to commit identity theft, financial fraud, or sell your data on the dark web.
Protecting your data isn’t just about privacy — it’s about safeguarding your financial stability, reputation, and peace of mind.
Common Cyber Threats That Target Personal Data
Before diving into protection strategies, it’s crucial to understand the major types of cyber threats that put your information at risk.
1. Phishing Attacks
Phishing is one of the most common techniques used by hackers to trick people into revealing personal information. These scams usually come in the form of emails, texts, or fake websites that appear legitimate. Once you click a malicious link or enter your credentials, hackers gain access to your accounts.
2. Malware and Ransomware
Malware (malicious software) infects your system to steal or destroy data. Ransomware is a specific type that encrypts your files and demands payment to unlock them. Both can cause severe damage to individuals and organizations alike.
3. Identity Theft
Cybercriminals use stolen data such as your name, address, or social security number to impersonate you. They can open bank accounts, take loans, or even commit crimes in your name.
4. Data Breaches
Data breaches occur when hackers gain unauthorized access to databases containing sensitive information. These breaches can expose millions of users’ personal details in one go.
5. Social Engineering
Social engineering manipulates human psychology instead of software vulnerabilities. Hackers may pose as trusted individuals or organizations to extract confidential information from you directly.
6. Weak Password Exploits
Many users still rely on simple, easy-to-guess passwords or reuse the same password across multiple accounts. Hackers use automated tools to crack weak passwords in seconds.
Step-by-Step Guide to Protect Your Personal Data
Now that you understand the threats, let’s explore practical strategies to protect your data and stay safe online.
1. Use Strong, Unique Passwords
A weak password is like leaving your door unlocked for hackers.
Create strong passwords that include a mix of uppercase letters, lowercase letters, numbers, and symbols. Avoid using obvious choices like “123456” or “password.”
Each account should have its own unique password. Consider using a password manager to generate and store complex passwords securely.
2. Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security beyond just a password. Even if hackers manage to steal your password, they won’t be able to access your account without the second verification step — such as a text code or authentication app.
Always enable 2FA on critical accounts like email, banking, and social media.
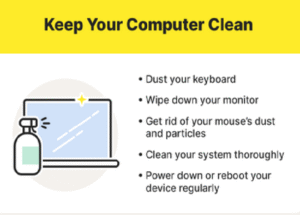
3. Keep Software and Devices Updated
Outdated software often contains vulnerabilities that hackers exploit. Regularly update your operating system, apps, and antivirus software.
Set your devices to automatic updates so you never miss important security patches.
4. Be Cautious with Emails and Links
Never click on suspicious links or download attachments from unknown senders.
Check the sender’s email address carefully — hackers often use addresses that look similar to legitimate ones.
If an email asks for sensitive information or claims urgent action, verify its authenticity directly through the official website or support channel.
5. Secure Your Wi-Fi Network
Your home Wi-Fi can be an easy target if not secured properly.
-
Change the default router password immediately.
-
Use WPA3 encryption for maximum protection.
-
Hide your network SSID if possible.
-
Avoid using public Wi-Fi for sensitive transactions; instead, use a VPN (Virtual Private Network) to encrypt your connection.
6. Use a Reliable Antivirus and Anti-Malware Tool
Antivirus software detects and removes harmful programs before they can damage your device or steal information.
Make sure to install a reputable antivirus solution and schedule regular scans.
Modern tools also offer real-time protection, email scanning, and safe browsing features.
7. Regularly Back Up Your Data
Data loss due to malware or ransomware can be devastating. Always back up your files to an external hard drive or a secure cloud service.
Set automated backups so you can restore your data quickly in case of a cyberattack or device failure.
8. Limit the Personal Information You Share Online
The more information you share publicly, the easier it becomes for hackers to target you.
Be mindful of what you post on social media — avoid revealing your location, birthday, or family details.
Review privacy settings on platforms like Facebook, Instagram, and LinkedIn to control who can view your personal data.
9. Encrypt Sensitive Files and Communications
Encryption scrambles your data, making it unreadable to unauthorized users.
You can encrypt important files stored on your computer or use secure communication apps that offer end-to-end encryption.
For emails, use encryption services like ProtonMail or built-in options such as S/MIME.
10. Use a VPN for Online Privacy
A Virtual Private Network (VPN) encrypts your internet traffic and hides your IP address, preventing hackers or advertisers from tracking your online activity.
Always use a trusted VPN, especially when accessing public Wi-Fi networks or handling confidential tasks like online banking.
11. Monitor Your Financial and Online Accounts
Keep a close eye on your bank statements, credit reports, and online accounts for any unusual activity.
If you notice unauthorized transactions or login attempts, change your passwords immediately and alert your bank or service provider.
12. Avoid Using Public Computers for Sensitive Tasks
Public computers in cafes, libraries, or hotels may have malware that records your keystrokes or stores your login data.
Avoid logging into personal or financial accounts from shared devices. If necessary, always clear the browser history and cache afterward.
13. Manage App Permissions
Mobile apps often request unnecessary permissions to access your contacts, camera, or location.
Review these permissions regularly in your phone’s settings and disable access that isn’t essential.
Only download apps from trusted sources like Google Play or the Apple App Store.
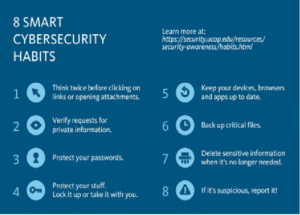
14. Stay Educated About New Cyber Threats
Cybersecurity is constantly evolving.
Follow credible cybersecurity blogs or experts to stay informed about new scams and threats.
Being aware of emerging attack methods gives you an advantage in recognizing and avoiding them.
15. Protect Your Cloud Storage
Cloud services are convenient but can also be targeted by hackers.
-
Use strong passwords and 2FA for your cloud accounts.
-
Avoid uploading highly confidential files without encryption.
-
Regularly review which devices are linked to your cloud account and remove any unfamiliar ones.
16. Safeguard Your Smartphone
Smartphones hold more personal data than ever before.
Set up a strong passcode or biometric lock (fingerprint or facial recognition).
Enable remote tracking and wiping features, so you can erase data if your phone is lost or stolen.
Never install apps from unknown sources or sideload APK files on Android devices.
17. Practice Safe Browsing Habits
Avoid visiting suspicious websites or clicking on ads that promise unrealistic rewards.
Always check for HTTPS in the website URL before entering personal or payment information.
Consider installing browser extensions that block trackers, pop-ups, and malicious scripts.
18. Secure Your Email Accounts
Your email is the gateway to most of your online accounts.
If hackers gain access to it, they can reset passwords and take over multiple services.
-
Use a strong, unique password.
-
Enable two-factor authentication.
-
Regularly clean up old emails containing personal data or attachments.
19. Manage Social Media Privacy Settings
Social platforms are goldmines for cybercriminals seeking personal information.
Regularly review who can view your posts, photos, and contact details.
Avoid accepting friend requests from strangers — they could be fake accounts used for phishing or social engineering attacks.
20. Secure Your Internet of Things (IoT) Devices
Smart home devices such as cameras, thermostats, and speakers often have weak security settings.
Change their default passwords, disable unnecessary features, and update their firmware regularly.
Keep these devices on a separate network from your main computer or phone for added safety.
What to Do If Your Data Has Been Compromised
Even with all precautions, breaches can happen.
If you suspect your data has been stolen or misused, take immediate action:
-
Change Your Passwords: Start with the affected account and then update others using similar credentials.
-
Notify Relevant Institutions: Contact your bank, email provider, or social platform to report the issue.
-
Check for Unauthorized Transactions: Review financial statements and freeze your credit if necessary.
-
Enable Account Recovery Options: Update your recovery email, phone number, and security questions.
-
Run a Full System Scan: Use antivirus software to remove any malware.
-
Monitor for Future Activity: Stay vigilant for any suspicious emails, login attempts, or data misuse.
Building a Cybersecurity Mindset
Cybersecurity isn’t a one-time action — it’s an ongoing mindset.
Adopting safe online habits, staying aware of the latest threats, and educating family members are key steps in creating a secure digital environment.
Remember, hackers target the easiest victims. By implementing strong security measures, you make yourself a much harder target.
Conclusion
Your personal data is your digital identity — once stolen, it’s almost impossible to reclaim completely.
Protecting it requires vigilance, awareness, and the consistent use of security tools and best practices. From using strong passwords and enabling two-factor authentication to keeping your devices updated and avoiding suspicious links, every small step counts toward stronger cybersecurity.
In a world where data is power, safeguarding your information is not just a choice — it’s a necessity. By following this complete cybersecurity guide, you can minimize risks, protect your identity, and enjoy the digital world with confidence.




Post Comment