The Future of Cybersecurity: Emerging Trends and Technologies
The pace of change in cybersecurity has never been linear. New technologies, shifting workplace models, and global conflicts continually reshape what defenders must protect and how they must do it. Today, three accelerants stand out: widespread cloud adoption, the explosion of connected devices, and the rapid emergence of powerful artificial intelligence systems. Together they create both unprecedented defensive capabilities and new attack surfaces.
This article explores the biggest trends and technologies shaping the future of cybersecurity, the risks and opportunities they bring, and practical guidance for organizations that want to stay ahead.
1. The Evolving Threat Landscape: Scale, Speed, and Automation
Attackers now operate at machine speed. Automated scanning, credential stuffing, and mass-targeted campaigns powered by AI mean attackers can probe millions of targets in minutes. The rise of Ransomware-as-a-Service and “fraud-as-a-service” lowers the technical barrier for criminals, while state-sponsored groups pursue strategic theft and disruption.
Traditional perimeter-based security and signature-based detection are no longer enough. Modern defense must be continuous, behavior-aware, and automated wherever possible, while still guided by human oversight for complex decisions.
2. Artificial Intelligence: Defender’s Greatest Asset and Attacker’s Most Powerful Weapon
Artificial intelligence (AI) has become both a defensive powerhouse and a potential threat multiplier.
How attackers use AI:
-
Craft convincing phishing and social-engineering messages at scale.
-
Automate reconnaissance and vulnerability scanning across millions of hosts.
-
Generate malware variants that evade traditional detection.
-
Launch multi-stage, adaptive attacks through AI-driven automation.
How defenders use AI:
-
Detect anomalies and novel threats using behavioral analysis.
-
Automate triage in Security Operations Centers (SOCs).
-
Perform large-scale threat hunting and pattern recognition.
-
Strengthen fraud and identity detection systems.
Organizations must strike a balance: leverage AI’s defensive benefits while enforcing governance, validation, and safety controls to avoid over-reliance or model manipulation. The ideal approach is “human-in-the-loop” — allowing AI to assist, but not fully replace, human judgment.
3. Zero Trust and Identity-First Security
The old “castle-and-moat” model — where everything inside the network is trusted — is obsolete. Zero Trust Architecture (ZTA) is now the gold standard. The core idea is simple: never trust, always verify.
Key components include:
-
Multi-Factor Authentication (MFA): Using phishing-resistant methods to verify users.
-
Micro-Segmentation: Dividing networks to prevent lateral movement.
-
Continuous Verification: Regularly checking user and device identity.
-
Least-Privilege Access: Giving users the minimum permissions needed.
By focusing on identity rather than location, Zero Trust ensures that even compromised devices or accounts have limited impact. Organizations adopting ZTA also gain resilience against ransomware and insider threats.
4. Cloud-Native Architectures, SASE, and XDR
As workloads migrate to cloud environments, traditional security models must evolve.
SASE (Secure Access Service Edge): Combines networking and security functions in the cloud, offering consistent policy enforcement for users everywhere. It simplifies remote security and eliminates the need for backhauling traffic through corporate data centers.
XDR (Extended Detection and Response): Integrates data from endpoints, networks, cloud workloads, and identities into one unified detection platform. It reduces alert fatigue, correlates signals, and enables faster, automated responses.
Cloud-Native Security Controls: Workload attestation, infrastructure-as-code scanning, and container runtime protection are becoming essential parts of DevSecOps pipelines.
Tip: Integrate these security tools during development (“shift-left” approach) rather than as afterthoughts during deployment.
5. Automation, Orchestration, and the Modern SOC
Security teams face overwhelming alert volumes and skill shortages. The solution lies in automation.
SOAR (Security Orchestration, Automation, and Response) tools automate repetitive triage tasks such as isolating endpoints, blocking malicious IPs, or resetting credentials.
AI-driven systems can summarize incidents, prioritize alerts, and even recommend actions — allowing analysts to focus on investigation and decision-making.
However, organizations must maintain human oversight. Automation errors can cause serious outages or misconfigurations. Therefore, automation should be implemented gradually and tested thoroughly.
6. IoT and OT Security: Bridging Digital and Physical Worlds
The expansion of the Internet of Things (IoT) and Operational Technology (OT) systems has introduced new vulnerabilities. Devices in smart homes, factories, and hospitals often lack proper security updates and are connected directly to networks.
Emerging best practices include:
-
Network Segmentation: Isolating IoT and OT systems from critical business networks.
-
Device Identity Management: Authenticating and verifying device firmware.
-
Continuous Monitoring: Detecting unusual device behaviors or command patterns.
As industries digitize, the line between IT and OT continues to blur. Cybersecurity for physical systems — power grids, manufacturing equipment, and transportation — will be as important as securing corporate servers.
7. Ransomware Evolution and Resilience
Ransomware remains one of the most profitable forms of cybercrime. Attackers now use double extortion tactics — stealing sensitive data before encrypting it, then threatening to leak it if ransom demands are not met.
Defensive strategies must focus on resilience, not just prevention:
-
Maintain immutable, offline backups.
-
Regularly test disaster recovery plans.
-
Implement network segmentation to contain infections.
-
Use endpoint detection and response systems to catch lateral movement.
Preparedness is key. Organizations that can restore operations quickly have greater leverage against extortion attempts.
8. Privacy, Regulation, and Cyber Insurance
As data privacy laws expand worldwide, businesses must prioritize compliance. Regulations now demand faster breach notifications, stricter data handling, and higher penalties for violations.
Cyber insurance has become another layer of protection — but insurers now require proof of strong security controls before offering coverage.
Companies must:
-
Align policies with evolving data protection laws.
-
Maintain up-to-date incident response and audit trails.
-
Demonstrate risk management for underwriting approval.
Cybersecurity is no longer only about protection — it’s also about legal and financial accountability.
9. Quantum Computing: Preparing for the Next Cryptographic Shift
Quantum computing poses a long-term risk to current encryption methods. Future quantum systems could break traditional algorithms like RSA and ECC, exposing sensitive data.
To prepare, organizations should begin transitioning toward post-quantum cryptography (PQC) — encryption algorithms resistant to quantum attacks.
Steps to take now:
-
Inventory where encryption is used across your systems.
-
Plan for crypto-agility, the ability to swap algorithms without major system overhauls.
-
Monitor progress in PQC standards from global bodies.
Although quantum computers capable of breaking encryption are still years away, data with long-term sensitivity — such as medical or legal records — needs protection today.
10. Supply Chain Security and Software Integrity
Modern organizations rely on thousands of third-party vendors and open-source libraries. A single compromised component can affect entire ecosystems.
To mitigate this, companies should:
-
Require Software Bills of Materials (SBOMs) from vendors.
-
Enforce code signing and version control for all internal and third-party software.
-
Continuously monitor dependencies for vulnerabilities.
Supply chain security is about visibility and accountability — knowing exactly what runs in your environment and where it came from.
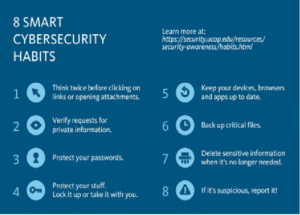
11. Workforce, Skills, and Human Factors
Human error remains one of the biggest cybersecurity risks. Whether it’s a misconfigured cloud service, a weak password, or a successful phishing attempt, people remain the primary target.
Organizations must cultivate a security-first culture through:
-
Regular awareness training and phishing simulations.
-
Role-based access control and least-privilege permissions.
-
Gamified learning and continuous education for employees.
Additionally, the cybersecurity skills gap remains wide. Companies can reduce this by investing in upskilling programs, leveraging AI-assisted tools to reduce workload, and hiring diverse talent with both technical and analytical skills.
12. Governance, Risk, and Metrics for the Future
Cybersecurity decisions must align with business outcomes. Boards now demand measurable results and accountability.
Effective governance involves tracking:
-
Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR).
-
Patch management efficiency.
-
Multi-Factor Authentication coverage.
-
Backup reliability and test results.
By connecting cybersecurity metrics with business impact, companies can justify budgets, improve resilience, and build trust with customers and regulators.
13. Practical Roadmap: Steps to Future-Proof Cybersecurity
-
Adopt identity-first controls: Deploy MFA and Zero Trust access for all high-value assets.
-
Invest in AI responsibly: Use AI for detection, but require human validation for critical actions.
-
Secure the development lifecycle: Integrate scanning and protection early in CI/CD pipelines.
-
Strengthen ransomware resilience: Keep offline backups and conduct regular recovery drills.
-
Implement Zero Trust for administrators: Apply continuous verification and privilege segmentation.
-
Enhance supply chain visibility: Demand SBOMs and enforce software integrity checks.
-
Automate securely: Test and validate every automated playbook with human oversight.
-
Measure what matters: Use metrics that reflect real business risk and resilience.
Conclusion — Security as an Ongoing Transformation
The future of cybersecurity will be defined by adaptability, intelligence, and collaboration. As threats evolve, so must the defenses. Artificial intelligence, Zero Trust architecture, and automation are no longer optional — they are fundamental to survival in the digital age.
However, technology alone cannot guarantee safety. True cybersecurity depends on a blend of advanced tools, skilled professionals, and a resilient mindset. The most secure organizations will be those that treat cybersecurity not as a cost, but as a continuous process of learning, adapting, and improving.
The coming decade will belong to those who understand that cybersecurity is not a one-time investment — it is the foundation of trust in the digital future.




Post Comment