Why Cybersecurity Is Important for Small Businesses in the Digital Age
In the digital age, technology has become the backbone of every modern business. Whether it’s managing online sales, storing customer data, or handling financial transactions, digital tools have revolutionized how small businesses operate. However, this digital transformation also brings new challenges—particularly in the area of cybersecurity.
Cybersecurity is no longer an issue that only large corporations or government institutions need to worry about. Small businesses, which often have limited resources and security measures, are now prime targets for cybercriminals. In fact, hackers often see small enterprises as “low-hanging fruit” because they are less likely to have robust defenses in place.
This article explores why cybersecurity is essential for small businesses, the threats they face, the consequences of a data breach, and practical strategies to protect their operations in today’s connected world.
1. Understanding Cybersecurity in the Context of Small Businesses
Cybersecurity refers to the protection of systems, networks, and data from digital attacks. These attacks aim to steal sensitive information, disrupt operations, or extort money from victims. For small businesses, cybersecurity involves implementing policies, technologies, and procedures to safeguard company assets from unauthorized access or damage.
Unlike large corporations with dedicated IT departments, small businesses often rely on basic security measures or even overlook cybersecurity entirely. Many owners assume their company is too small to attract hackers. However, statistics show that nearly half of all cyberattacks target small businesses because they tend to have weaker protection and are easier to exploit.
2. Why Small Businesses Are Attractive Targets for Cybercriminals
Small businesses are not immune to cybercrime—in fact, they are often more vulnerable. Here are some key reasons why attackers focus on them:
a. Limited Security Infrastructure
Small companies usually have tight budgets and limited IT expertise. They may not invest in advanced firewalls, intrusion detection systems, or encryption technologies, making them easy targets.
b. Valuable Data
Even small businesses handle sensitive information such as customer names, addresses, payment details, and employee records. Hackers can use or sell this data on the dark web for financial gain.
c. Weak Password Policies
Many small organizations lack strict password protocols. Employees often reuse simple passwords, which makes it easier for attackers to gain access through brute force or phishing.
d. Third-Party Vulnerabilities
Small businesses frequently use third-party vendors, cloud services, and payment processors. If these partners experience a breach, the small business may also be affected.
e. Lack of Cyber Awareness
Many small business owners underestimate cyber risks. Employees might unknowingly click on phishing emails or use unsecured networks, creating openings for hackers.
3. Common Types of Cyber Threats Facing Small Businesses
Cyber threats come in many forms, and understanding them is the first step toward prevention. Below are the most common attacks that target small businesses:
a. Phishing Attacks
Phishing is one of the most widespread cyber threats. It involves sending fake emails or messages that trick users into revealing personal information or clicking malicious links. These attacks often appear legitimate, mimicking trusted brands or internal company communications.
b. Ransomware
Ransomware encrypts a company’s data, rendering it inaccessible until a ransom is paid to the attacker. This can cripple business operations and lead to significant financial losses. Small businesses often lack proper backups, making them more likely to pay the ransom.
c. Malware
Malware, short for malicious software, includes viruses, trojans, and spyware. Once installed, malware can steal information, disrupt operations, or provide attackers with remote access to systems.
d. Insider Threats
Not all threats come from outside. Employees or contractors with access to sensitive systems can intentionally or accidentally expose data. Insider threats can be due to negligence, mistakes, or malicious intent.
e. Denial-of-Service (DoS) Attacks
In a DoS attack, hackers flood a company’s website or server with traffic, overwhelming it and causing downtime. This disrupts customer access and can result in lost revenue.
f. Business Email Compromise (BEC)
BEC attacks involve impersonating executives or business partners to trick employees into transferring money or disclosing confidential information.
4. The Consequences of a Cyberattack on Small Businesses
A successful cyberattack can be devastating for small businesses, leading to financial, operational, and reputational damage. Some of the most severe consequences include:
a. Financial Losses
Cyberattacks often result in direct monetary losses through theft or ransom payments. Additionally, businesses may face costs for system repairs, legal fees, and regulatory fines.
b. Damage to Reputation
Losing customer trust can be more harmful than financial loss. A single data breach can tarnish a company’s image, driving customers away and discouraging new clients from engaging.
c. Business Disruption
Cyber incidents can halt operations for days or weeks. For small businesses that depend on daily transactions, downtime can lead to lost revenue and missed opportunities.
d. Legal and Compliance Issues
Many countries have strict data protection laws. If a small business fails to secure customer information, it could face penalties for non-compliance with regulations such as GDPR or other local data privacy laws.
e. Loss of Intellectual Property
Small businesses often rely on innovation and proprietary ideas. A cyber breach could expose valuable trade secrets, giving competitors or criminals an unfair advantage.
5. Benefits of Implementing Strong Cybersecurity Practices
Investing in cybersecurity not only protects against threats but also provides long-term business benefits. Here’s how strong cybersecurity practices can help small businesses:
a. Protects Customer Data
Customers expect their personal and financial information to be safe. Implementing robust cybersecurity safeguards builds confidence and loyalty.
b. Enhances Business Reputation
A secure company earns credibility in the marketplace. Cybersecurity demonstrates professionalism and reliability, attracting more clients and partnerships.
c. Ensures Business Continuity
With proper backup systems and disaster recovery plans, businesses can quickly resume operations after an attack, minimizing downtime.
d. Reduces Financial Risks
Preventing cyber incidents saves businesses from the costly aftermath of data breaches and ransom payments.
e. Increases Competitive Advantage
Many customers and suppliers prefer to work with secure companies. Demonstrating strong cybersecurity can help a small business stand out in a competitive market.
6. Key Cybersecurity Measures Every Small Business Should Implement
While small businesses may not have large budgets, they can still adopt effective cybersecurity practices to protect their operations. Below are essential measures every small business should take:
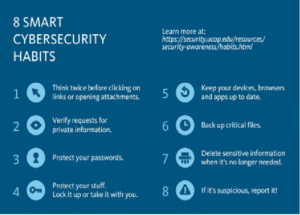
a. Educate Employees
Human error is one of the biggest cybersecurity risks. Regular training on recognizing phishing attempts, creating strong passwords, and handling sensitive data can significantly reduce risks.
b. Use Strong Passwords and Multi-Factor Authentication (MFA)
Encourage employees to use complex passwords and implement MFA wherever possible. MFA adds an extra layer of protection by requiring a second form of verification.
c. Keep Software and Systems Updated
Outdated software often contains vulnerabilities that hackers can exploit. Regularly update operating systems, antivirus programs, and applications.
d. Install Antivirus and Anti-Malware Tools
Reliable security software can detect and block malicious programs before they cause harm.
e. Backup Data Regularly
Maintain secure backups of critical data, ideally stored offsite or in the cloud. This ensures data recovery in case of ransomware or accidental deletion.
f. Secure Wi-Fi Networks
Use encrypted Wi-Fi with strong passwords. Separate guest networks from internal company systems to prevent unauthorized access.
g. Limit Access to Sensitive Information
Only grant employees access to data necessary for their roles. Implement role-based permissions to minimize the impact of a potential breach.
h. Develop an Incident Response Plan
Prepare a step-by-step plan for responding to cyber incidents. This plan should include containment, investigation, communication, and recovery strategies.
i. Use Firewalls and Encryption
Firewalls act as barriers between your network and potential intruders, while encryption ensures that data remains unreadable to unauthorized users.
7. The Role of Cloud Security in Small Business Protection
Many small businesses rely on cloud-based services for storage, collaboration, and customer management. While cloud computing offers flexibility and cost savings, it also introduces new security considerations.
To protect cloud environments:
-
Choose reputable cloud service providers that comply with industry security standards.
-
Use encryption for data at rest and in transit.
-
Regularly review user permissions and access logs.
-
Enable automatic updates and data backup features.
By following these steps, small businesses can enjoy the benefits of the cloud while minimizing risks.
8. How Cyber Insurance Can Help Small Businesses
Cyber insurance is becoming an essential part of modern business protection. It provides financial coverage for losses resulting from cyber incidents such as data breaches, ransomware, or business interruptions.
Benefits of cyber insurance include:
-
Financial protection against legal fees, investigations, and customer notifications.
-
Reputation management through support for public relations and crisis response.
-
Business recovery assistance to help companies restore systems and operations.
For small businesses, having cyber insurance can be the difference between recovery and permanent closure after a major attack.
9. Building a Cybersecurity Culture Within the Organization
Cybersecurity isn’t just a technical issue—it’s a cultural one. A business can have the best technology, but if employees don’t follow safe practices, breaches can still occur. Creating a cybersecurity culture means making security part of everyday business behavior.
Steps to build a strong cybersecurity culture include:
-
Encouraging open communication about potential threats.
-
Recognizing and rewarding employees who follow security best practices.
-
Conducting regular security audits and simulations.
-
Appointing a cybersecurity champion to oversee training and compliance.
When every team member understands their role in protecting the company, the entire organization becomes stronger.
10. The Future of Cybersecurity for Small Businesses
As technology evolves, so do cyber threats. The rise of artificial intelligence (AI), the Internet of Things (IoT), and remote work has expanded the attack surface for businesses. In the future, small companies will need to adopt more sophisticated security tools, such as AI-driven threat detection and automated response systems.
Moreover, cybersecurity regulations will continue to tighten, making compliance a legal necessity. Businesses that invest in security early will be better prepared to meet future challenges and build sustainable, trustworthy brands.
Conclusion: Cybersecurity Is No Longer Optional
In today’s digital economy, cybersecurity is not a luxury—it’s a necessity. Small businesses are increasingly reliant on technology to drive growth, manage customers, and compete in global markets. However, this dependence also exposes them to a range of cyber risks that can have devastating consequences if ignored.
By understanding these risks and taking proactive steps—such as training employees, implementing strong defenses, securing cloud systems, and investing in cyber insurance—small businesses can safeguard their future.




Post Comment